The number of threats to our privacy is beyond what we can count and new ways appear every day to spy on us or try to deceive us to obtain our data.
Today we will talk about stalkerware, a variant of malware that is becoming fashionable and that will soon be present among us as an everyday thing.
What is stalkerware?

Stalkerware is commercially available software used to secretly spy on someone else's private life via a smart device.
The word derives from the English "stalker" (stalker) and therefore it is spy programs that are installed on smart devices (such as a smartphone or tablet) to record activities, both in space and time and in one's own device, in person .
Other ways to call it, since they are its main applications, are "spouseware", "virus stalker" and so on.
In Europe, seven out of ten women they have undergone cyberbullying they also suffered at least one form of physical or sexual violence from your partner. Likewise, the 71% of domestic abusers monitor the online activity of women and the 54% you have trace of cell phones of the victims with stalkerware software.
How is stalkerware installed?
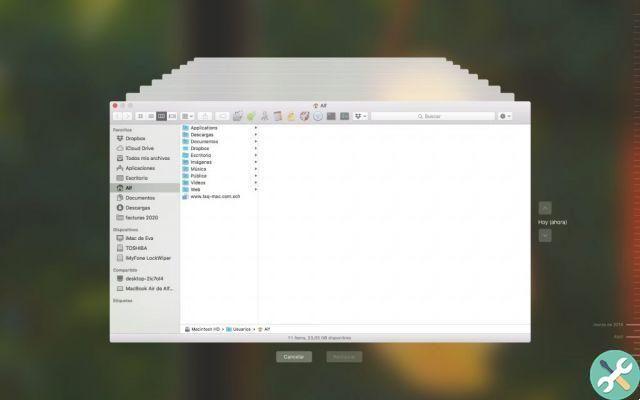
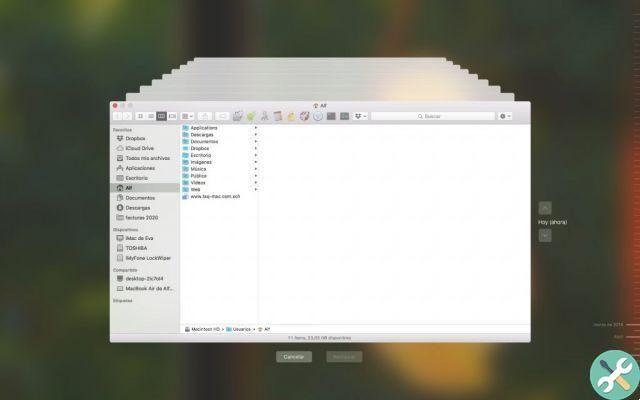
The difference with other malware is that it requires physical access to the device and knowledge of the keys to access the content.
It involves getting hold of the smartphone or tablet, installing a spy program and linking it to another program that the stalker has on their device.
Once connected, they start receiving location data, written messages, notifications (social networks, etc.), photos, videos and even recordings of conversations made on the device.
How was stalkerware born?

It could be said that stalkerware is something that was born with a legitimate (or at least not perverse) purpose and that it ended up being used for something almost completely the opposite.
Its origin is in the applications that were developed so that parents could control their children, in terms of location and routes, the pages they visited, the photos they sent and received.
It is true that one could have a long conversation about the education that parents should have given their children prima di put a cellphone or tablet in their hands, but it is also true that many times the bad guys are crafty enough to engage their business in an aura of naivety and innocence so that babies or teens are unaware of what they are into. they are hunting until it is too late.
In any case, parents' apprehension (justified or not) that their children had gotten into some trouble or that something had happened to them back from school led to the development of applications that would let them know what they were doing. or where without users know.
It didn't take long to deflect that focus on husbands, partners, or just plain obsessives harassing, stalking, and threatening people without their consent or knowledge.
So while it may be legal to install this type of software on a device used by a minor, it is totally illegal (and immoral) to install it on a phone or tablet without the consent of its owner (of age).
Partnership against stalking: the EU takes action on this
The EU launched the DeStalk project to tackle cyber violence and gender stalkerware, in which the cybersecurity community, civil society, research organizations and government authorities collaborate.
DeStalk addresses the issues of cyberviolence and stalkerware which represent new, widespread and hidden forms of GBV.

Within two years, the European project team, made up of leading experts in gender-based violence and cyber security, will jointly develop the training content and then train professionals in victim support services and programs for aggressors in health and social services.
It will also train key stakeholders from regional authorities and governments to raise public awareness and take action against cyber violence.
Since the beginning of 2021, five partners - the European network for work with perpetrators of domestic violence, the Blanquerna Foundation, Kaspersky, Una Casa per l'Man and the Veneto Region - have joined forces to work on the European Union project «DeStalk », Supported by the European Commission through its Rights, Equality and Citizenship Program.
In addition to this association, since 2019 there is the Coalition Against Stalkware, which represents the union of advocacy groups, software developers, security companies and survivors to put an end to abusive technology and software.

Can stalkerware be installed on an iPhone?
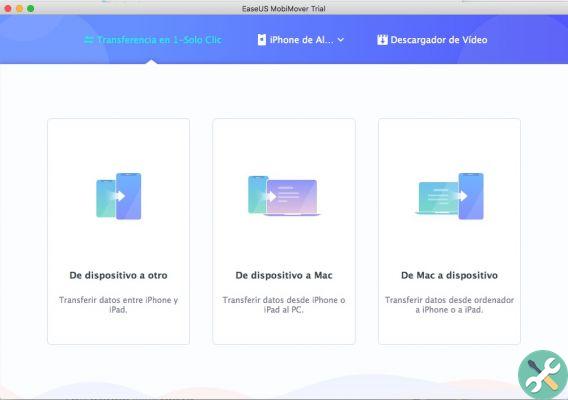
In abstract terms, the search app, coupled with the "Family Sharing" plan that Apple has on its devices, is a form of stalkerware - very limited.
Search allows us to see the location of people we have added to our family, and we may share multiple files such as photos, App Store purchases, books, etc.
However, that an external app can do this is much more complex, since iOS applications work in a "sandbox" mode, ie isolated in their space, so that one does not have access to what the other is doing.
Also, to be able to access what the microphone, camera, etc. the user must expressly authorize their access. Theoretically, the same "stalker" could do this at the same time as installing the application, but it is unlikely to cover all options.
If you have questions about spyware installed on your phone, we recommend that you read the guide Apple has posted on how to strengthen the privacy of your device if you feel in danger.
For these applications to work, the iPhone has to be jailbroken, which is increasingly difficult, which is why these types of applications are normally installed and run on Android devices.






![Google also wants your Apple News [Updated] [2]](/images/posts/943dc0d8f28fcc4bc16fa30ed6d71f6a-0.jpg)



![Apple Vice Presidents Talk About Development of M1 for Mac [Updated]](/images/posts/c6254b668e5b3884d6b6338ccb8a02ff-0.jpg)